One of the hard truths about cybersecurity is that security breaches are not always obvious. Suppose for a moment that an attacker has gained access to your Microsoft 365 administrative credentials. While the attacker could use those credentials to immediately engage in cyber vandalism, it is far more likely that the credential theft will go unnoticed for a time.
Attackers often will log in, observe the organization’s activities and steal data. They know that these types of activities are unlikely to draw attention, whereas if the attacker began deleting data or planting ransomware, the organization would quickly know something was up.
Microsoft 365’s My Sign-ins Page
The easiest way to tell if an attacker has used your Microsoft 365 administrative privileges is to look for indications in the logs.
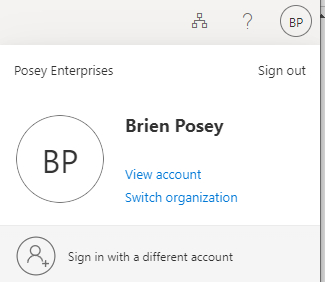
You can access these logs by signing into Microsoft 365, then going to the My Account page. You can get to the My Account page by clicking on your profile located in the upper-right corner of the page. Next, click on the “View Account” option. The two screenshots below show the My Account link and the page itself.

The My Account page includes a section called My Sign-ins, located in the lower-right corner. Click “Review Recent Activity” for an overview of recent Microsoft account sign-in activity.

The overview provides helpful information about sign-in events. In most cases, you can see the date and time of a sign-in, as well as the sign-in location. It can even show a generalized map of the area where the sign-in event occurred. Depending on the activity, the page may display information about the operating system and browser used for the login, the associated IP address, the applications that were accessed, and the account name.
In the above screenshot, I obscured the IP address in the account name, but you can at least get an idea of what the page will look like.
Detect Unusual Sign-In Activity
When examining the Review Recent Activity list, you should be able to get a sense of what is normal for your organization. In my case, for example, I would expect to see a lot of sign-ins from South Carolina since I live in South Carolina.
What if you see logins that you don’t recognize? If you see unusual sign-in activity, it doesn’t necessarily mean that you have had a security breach (although it could mean that). The first thing you should do is check to see if the logins were successful. In the previous screenshot, you can see that Microsoft 365 will display information about whether logins were successful.
If a suspicious login was successful, then the next thing that you should do is determine if there is a rational explanation. For example, if you sign in with a VPN, then the VPN probably has a different IP address than what you would usually see, which could explain the suspicious-looking login.
Mobile devices can also be tied to unusual sign-in activity. As I prepared this article, I noticed some logins from California on my account. I haven’t been to California recently, so these logins got my attention. The very first thing that I did was Google the IP address associated with the logins. When I did, I realized that the IP addresses belong to T-Mobile, which happens to be the cellular provider I use. At that point, I knew it was likely my mobile device caused these California-based logins. It remained possible that the logins could be attributed to a bad actor, however. To find out, I turned off my mobile device and rebooted. I then logged back in and synchronized my Exchange mailbox to see if a login event was recorded on the My Sign-ins dashboard. As you can see in the image below, I did indeed log a sign-in event from California.

In this case, nothing was amiss. If you do discover that a sign-in was unauthorized, you should immediately create a new password.





